Cracking passwords the Web application way
Don't make the mistake of thinking your Web site is secure just because it uses SSL. If you don't have proper login controls in place, attackers can crack passwords and get into the application.
 |
|
How do your Web applications stand up to authentication attacks? Have you taken the time to analyze just how your account passwords can be cracked? Sure, passwords and Web login mechanisms are boring compared to the fun you can have testing for SQL Injection and cross-site scripting (XSS), but they're still a big weakness that deserve ongoing attention.
A lot of Web sites are deemed "secure" as long as Secure Sockets Layer (SSL) is being used. Ha! If only it were that simple. Unlike operating system and database accounts that have strong password controls that are simple to implement and enforce, Web application authentication controls are all over the map.
This mish-mash of security is the basis of Web login vulnerabilities and why passwords are often easily cracked. Be it form-based, HTTP Basic, or NT LAN Manager (NTLM) (the three main types of authentication that most applications use), any of them can be cracked when proper login controls are not in place. And they're usually not.
Some common vulnerabilities that I see that can easily lead to an attacker cracking Web passwords include the following:
- No intruder lockout after a certain number of failed attempts
- Intruder lockout time that's too short
- Allowing simultaneous logins from the same or multiple hosts
- Transmitting login traffic via HTTP and not using SSL (I know that's a slight contradiction to my typical stance that 'SSL adds little value,' but as you'll see below, it can be a problem.)
|
|||||||||||||||||
I'm surprised to find so many Web applications that have those general weaknesses. Be it in-house Web applications, off-the-shelf Web software for email/ecommerce/etc., or Web interfaces on critical network infrastructure hosts such as firewalls, routers, and physical access controls systems, the fact is they're everywhere. And they're not being properly tested for weaknesses. With the right tools, malicious intent and a relatively small amount of time, attackers can compromise your Web accounts, and odds are no one will ever know about it until it's too late.
To begin performing your own password cracking, you need to know which systems are available to test. You'll know the obvious ones, but you may not have thought about all of the other Web-enabled systems in your environment. All you need is a basic port scanner such as the tried-and-true (and free) SuperScan. On the commercial side, Web vulnerability scanner products often have their own built-in Web finder tools, such as SPI Dynamics' WebInspect with its Web Discovery and Acunetix's Web Vulnerability Scanner with its Target Finder (shown below).
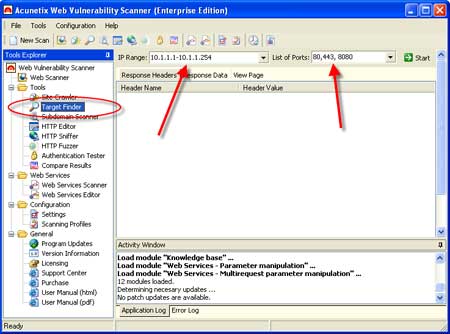 |
Figure 1: Acunetix Web Vulnerability Scanner's Target Finder for discovering live Web systems
As far as cracking goes, there are plenty tools that work well. I like the free Brutus AET2 tool (shown below).
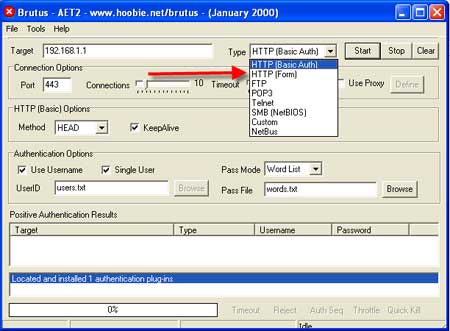 |
Figure 2: The free Brutus AET2 tool for cracking Web passwords
Brutus can be used to crack both HTTP Basic and form-based passwords using dictionary attacks and brute-force attacks, which really sets it apart from the other tools. Like most password-cracking tools, it's as simple as entering the IP address, selecting a few options, and clicking Start.
If you're UNIX/Linux-savvy or have Cygwin on your system, there's the free THC-Hydra tool, which can perform cracks against HTTP-NTLM authentication and more. There are also commercial tools for cracking various types of Web authentication mechanisms, such as Web Brute, which is packaged with WebInspect as shown below.
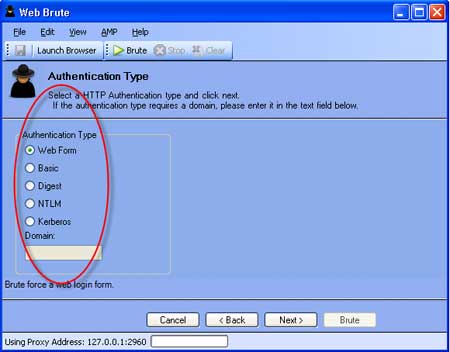 |
Figure 3: HP's commercial Web Brute tool for cracking Web passwords
Finally, the free Cain and Abel tool goes about "cracking" Web passwords a different way. Cain's core function is that of a network analyzer. When connected to a span/mirror port on an Ethernet switch, it will capture all cleartext Web passwords (among others) right off the wire as shown in the figure below.
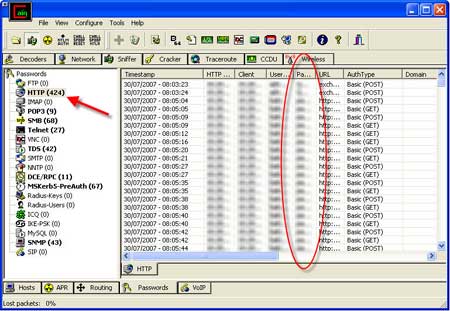 |
Figure 4: Cain's password sniffer for capturing Web passwords traveling across the network
I know; most people aren't going to have free access to your Ethernet switches, but they don't need to. All an attacker has to do is enable ARP poison routing in Cain (easily accomplished in a matter of seconds) and voila -- he now has the equivalent of full access to all network traffic from the otherwise basic Ethernet port he's connected to.
|
||||
So, there you have it -- good tools and easy techniques for cracking Web application passwords. As simple as it is, it's important to remember that Web password cracking shouldn't be taken lightly. Treat this as a formal penetration test and carefully plan things out, including getting permission and having a fall-back plan. You don't want to create trouble such as locking Web accounts or creating denial-of-service conditions on the Web server. Proceed with caution and a good set of dictionaries -- such as the ones here and here -- and you'll be on your way towards better Web site security.
-----------------------------------------
About the author: Kevin Beaver is an independent information security consultant, speaker, and expert witness with Atlanta-based Principle Logic, LLC where he specializes in performing independent security assessments. Kevin has authored/co-authored six books on information security, including Hacking For Dummies and Hacking Wireless Networks For Dummies (Wiley). He's also the creator of the Security On Wheels blog and information security audio books providing security learning for IT professionals on the go. Kevin can be reached at [email protected].







