Open Web Application Security Project (OWASP)
What is the Open Web Application Security Project (OWASP)?
The Open Web Application Security Project (OWASP) is a nonprofit foundation that provides guidance on how to develop, purchase and maintain trustworthy and secure software applications. OWASP is noted for its popular Top 10 list of web application security vulnerabilities.
The OWASP Top 10 list of security issues is based on consensus among the developer community of the top security risks. It is updated every few years as risks change and new ones emerge. The list explains the most dangerous web application security flaws and provides recommendations for dealing with them.
OWASP seeks to educate developers, designers, architects and business owners about the risks associated with the most common web application security vulnerabilities. OWASP supports both Open Source and commercial security products. It is known as a forum in which security experts and information technology professionals can network and build expertise.

What is the OWASP Top 10 and how does it work?
The OWASP Top 10 is a list of the 10 most important security risks affecting web applications. It is revised every few years to reflect industry and risk changes. The list has descriptions of each category of application security risks and methods to remediate them.
OWASP compiles the list from community surveys, contributed data about common vulnerabilities and exploits, and vulnerability databases.
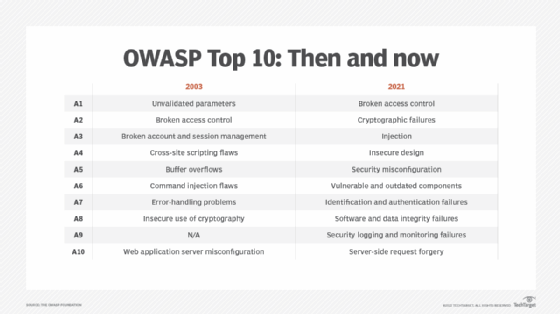
The first version of the OWASP Top 10 list was published in 2003. Updates followed in 2004, 2007, 2010, 2013 and 2017. The most recent update was published in 2021.
Risks that make the list at any point are identified by their rank on the list and the year of the list. So, for example, the top security risk in the most recent list is broken access control. It is assigned the identifier of A01:2021. "A" is for AppSec, followed by its rank in the list, the ":" symbol and the year.
The numbering system helps refer to prior versions of risks, especially where the name of a category has changed or categories have merged or expanded.
OWASP Top 10 security risks, 2021
The top 10 security risks OWASP identified in its 2021 update are the following:
- A01:2021 Broken access control. With these vulnerabilities, attackers can bypass access controls by elevating their own permissions or in some other way. This approach gives unauthorized users access to data or systems. Broken access controls have become the top category of security risk for web applications rising from the fifth spot in 2017. This category was created in 2017 by merging two other categories: missing function access control and insecure direct object references.
- A02:2021 Cryptographic failures. These risks happen when cryptographic methods aren't used appropriately to protect data. These vulnerabilities include the use of cryptographic ciphers that are obsolete, cryptographic protocols that aren't implemented correctly and other issues related to cryptographic controls. This category was previously known as sensitive data exposure. OWASP changed the name to reflect the importance of cryptographic failures in enabling exposures of sensitive information.
- A03:2021 Injection. These vulnerabilities let attackers insert data in an application that includes malicious commands, redirects data to a malicious website or changes the application itself. The most common type of flaw, Structured Query Language injection, still represents an important vector for attacks. Remediation for injection attacks is to explicitly authenticate all untrusted data, especially data submitted by end users. This category was expanded to include the cross-site scripting category in the 2021 Top 10 list.
- A04:2021 Insecure design. Risks in this category come from system architecture design flaws. These issues happen when an application is designed around insecure processes. For example, these problems arise when an application is developed using an authentication process that isn't secure or a website isn't built to prevent bots.
- A05:2021 Security misconfiguration. In this category, it is the problems with the security configuration of an application that facilitate attacks. For example, an application might not filter incoming packets correctly and could enable use of a default user ID, password or authorization. This category was expanded in 2021 to include the Extensible Markup Language external entities category.
- A06:2021 Vulnerable and outdated components. These risks arise when developers use software components with vulnerabilities in applications. They also appear when software is unpatched, out of date or similarly compromised. Vulnerable components include libraries, frameworks, application programming interfaces (APIs) or other modules. If the underlying operating system or a program interpreter is unpatched, it could cause these problems. Out-of-date APIs and software libraries can also create these issues for the application.
- A07:2021 Identification and authentication failures. These vulnerabilities include authentication issues that enable credential stuffing and brute-force attacks. The category also includes applications that don't use multifactor authentication and don't invalidate user sessions that have expired or are not active. In 2017, these risks were referred to as broken authentication. The category was renamed in 2021 to include broken authentication and broken session management.
- A08:2021 Software and data integrity failures. This category encompasses application code and infrastructure that doesn't fully protect software or data integrity. For example, issues can occur if digital signatures aren't used when software updates are installed. This category was expanded in 2021 to include the insecure deserialization category.
- A09:2021 Security logging and monitoring failures. These vulnerabilities occur when a system isn't adequately monitored to detect and respond to attacks and logs kept of these events. Before 2021, this category was called insufficient logging and monitoring. The name change reflects the expansion of the category to include more types of monitoring and logging failures.
- A10:2021 Server-side request forgery. Applications must perform adequate validation of user-provided resources to prevent these attacks. Threat actors can use these vulnerabilities to make applications access malicious websites.
What other projects has OWASP published?
OWASP has other projects besides its Top 10 list. Its three categories of other tool, document and code library projects are the following:
- tools and documents used to find security-related design and implementation flaws;
- tools and documents used to guard against security-related design and implementation flaws; and
- tools and documents used to add security-related activities into application lifecycle management.
OWASP has 250 active projects. Of those, 18 are considered flagship projects. The OWASP Top 10 is the best known, but others include the following OWASP programs:
- Amass is a tool for in-depth domain name system enumeration, attack surface analysis and external asset discovery.
- Application Security Verification Standard is a framework for testing web application security controls and a set of secure development requirements.
- Cheat Sheet Series is a set of guides for good security practices for application development.
- CSRFGuard is a library that implements patterns that can minimize the risk of cross-site request forgery, also known as CSRF, attacks.
- CycloneDX is a standard for bill of materials security and supply chain component analysis.
- Defectdojo is a vulnerability management tool for the security testing
- Dependency-Check does dependency checking for vulnerabilities as part of software composition analysis.
- Dependency-Track is a component analysis platform that identifies risks in the software supply chain.
- Juice Shop is an example web application designed to incorporate all of the underlying vulnerabilities listed in the OWASP Top 10 list. It's written entirely in JavaScript and provides a hacking target for penetration testers and other security professionals.
- Mobile Security Testing Guide is a set of standards for mobile application security testing, security requirements and verification.
- ModSecurity Core Rule Set is a set of attack detection rules used in web application firewalls.
- Offensive Web Testing Framework is a framework for penetration testing.
- Software Assurance Maturity Model analyzes and improves software security throughout the software development lifecycle.
- Security Knowledge Framework is a web application that explains how to use secure coding principles in different programming languages.
- Security Shepherd is a security training platform for web and mobile applications.
- Web Security Testing Guide is a comprehensive guide to security testing for web applications and web services.
- Zed Attack Proxy is a web app scanner used for penetration testing, as well as for training. It is released under the Apache open source license.
The history of OWASP
OWASP has evolved from its beginnings as an online community project in 2001 to its current status as a global force for web application security. The following are some key milestones in OWASP history:
- 2001. OWASP is announced on the WebAppSec mailing list, and founder Mark Curphey registers the owasp.org domain.
- 2003. The OWASP Top 10 is published. The No. 1 entry is broken access control.
- 2004. OWASP is incorporated as a U.S. nonprofit charity. The second version of the OWASP Top 10 list is published.
- 2007. The third version of the OWASP Top 10 list is published.
- 2010. The fourth version of the OWASP Top 10 list is published.
- 2013. The fifth version of the OWASP Top 10 list is published.
- 2016. The OWASP Mobile Top 10 list is published.
- 2017. The sixth version of the OWASP Top 10 list is published.
- 2019. OWASP publishes the first version of a new list: the OWASP API Security Top 10. It focuses on the top API vulnerabilities and security risks.
- 2021. The latest version of the OWASP Top 10 list is published.
Some organizations use the OWASP Top 10 as a security framework. Find out more about choosing the right security framework.







